As Microsoft has recently made frequent changes to the semi-annual feature updates (function updates), it is not easy to keep track of everything.
I would therefore like to clarify a few points in this article:
1. definition/general information
Microsoft has renamed the Update Channels. Previously there was "Current Branch (CB)" and "Current Branch for Business (CBB)". This became the semi-annual channel.
CB -> semi annual channel (targeted)
CBB -> semi annuel channel
In the targeted channel, the feature updates are available immediately after the release - as the name suggests, approximately every six months. In the semi annual channel without targeted, the updates are only offered for installation after around four months. I will go into the options for influencing this in point 2.
Windows 10 home edition users are inevitably on the "targeted" channel and always receive the updates immediately.
2. defer feature updates
The most convenient way to influence the installation time is via group policy. There are GPOs for this in the "Windows Update for business" area. Can be found on a German system under:
Computer configuration\Administrative templates\Windows components\Windows Update\Windows Update for Business
-> "Select time for receiving pre-release versions and function updates"
Feature updates can be postponed for up to 365 days. Cumulative updates for a maximum of 30 days.
2.1 CAUTION Trap: Dual Scan Client
If, at the same time as the above-mentioned GPO, e.g. for WSUS, the guideline "Specify internal path for the Microsoft update service" is configured, the Dual Scan Client which was introduced with version 1607. From now on, this searches automatically or by clicking on "Check online for updates from Microsoft Update." As a result, clients may receive feature updates unintentionally or too early. Details can be found in the Technet blog.
With the installation of the update KB4034658or updates in general after July 18, 2017, a group policy is installed on the Windows client that prevents this behavior. In German it has the unwieldy name: "Do not allow update deferral policies that check Windows Update" (Computer Configuration\Administrative Templates\Windows Components\Windows Update)
With the help of this guideline, feature updates can be postponed as desired without the risk of unwanted installation.
3. distribute feature updates with WSUS
At this point I would like to quote a document from Microsoft regarding the requirements.
It bears the name: Deploying Windows 10 updates with Windows Server Update Services (WSUS) You will find a lot of useful information here. Including the necessary requirements.
"In order for WSUS to manage and deploy Windows10 feature updates, you need WSUS4.0, which is available in the Windows Server2012 R2 and Windows Server2012 operating systems. In addition to WSUS 4.0, you must also install the patches KB3095113 and KB3159706 on the WSUS server."
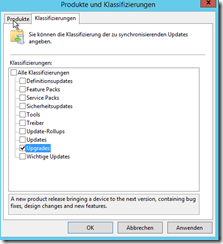
In order for WSUS to provide the feature updates, only these two settings are required under the item Products and classifications necessary.
- Products: Windows 10
- Classifications: Upgrades
4. prevent feature updates
The easiest way to keep feature updates away from clients is not to make them available via WSUS. This means not releasing them for installation or not downloading the "upgrades" from Microsoft in the first place.
However, as described above, please note that the following two GPOs are set to not configured:
- "Select when receiving function updates" or with the newer name "Select time for receiving pre-release versions and function updates"
- "Select when receiving quality updates"
In principle, feature updates should not be held back for too long, as each Windows version is only supplied with patches for 18 months.
5. windows 10 LTSB (Long-Term Servicing Branch)
For all those for whom the many updates/upgrades are too much of a good thing, there is also the LTSB version. Here is a brief summary of the most important information.
- is only available with a volume license agreement
- there are no feature updates for this version
- five years of patches, even for non-critical bugs
- 10 years of patches for security-related bugs
- New LTSB version every two to three years
- Hardware support is only guaranteed for devices that are on the market at the time of release

@Michael: Ich verwende DesktopCentral von ManageEngine für das Patchmanagement. Funktioniert super.
@Simon
Danke für die Info. Genau das mache ich zur Zeit… Ist halt bei einigen hundert PCs aber nicht so lustig :-).
Ich werde mir da mal was mittels Script und Tasks überlegen.
Oder hat da schon jemand was?
Schönes Wochenende an alle
Grüße
Michael
@Michael
Kleiner Tipp: größere Updates für das Wochenende planen und die Kisten per WoL starten und neustarten lassen. :)
Hallo David,
Erstmal danke für den super Artikel.
Kurze eine Frage:
Unterscheiden sich die Feature-Updates über WSUS von jenen, die ich über den „normalen“ Weg herunterlade und installiere? Größe, Installationsdauer…..
Ich glaube für jeden von uns ist es fast eine Zumutung diese großen Dinger zu installieren und den Benutzer zu erklären, warum er am nächsten Tag seeeeeehr lange warten muss :-).
Danke für die Hilfe
Beste Grüße
Michael
Hallo Michael,
freut mich, dass Dir der Artikel gefällt.
Soweit ich weiß, sind die Feature-Updates über WSUS identisch.
Gruß, David